#get #create #date #time https://istorik.net/uploads/slava-ukraini.jpg
NSA CIA Request
Posts 1 to 25 of 25
Share220-12-2025 20:53:45
#get #image #link https://officiel-online.com/wp-content/ … amed-8.jpg
#image #multiplicate #random #link
Share320-12-2025 20:55:27
This a bloodsucker или кровосися, точнее любительница блуда, блудница ( почти библейная ), заблудившаяся, пошла в лес без путника )))))))
Share420-12-2025 20:57:52
#get #phonenumber #accounter #scan #image
#phonenumber #multiplicate #random #link
Share520-12-2025 21:12:34
#get #phonenumber #accounter #scan #image
#phonenumber #multiplicate #random #link
Share620-12-2025 21:16:41
#make #handjob ))))
#compare #model
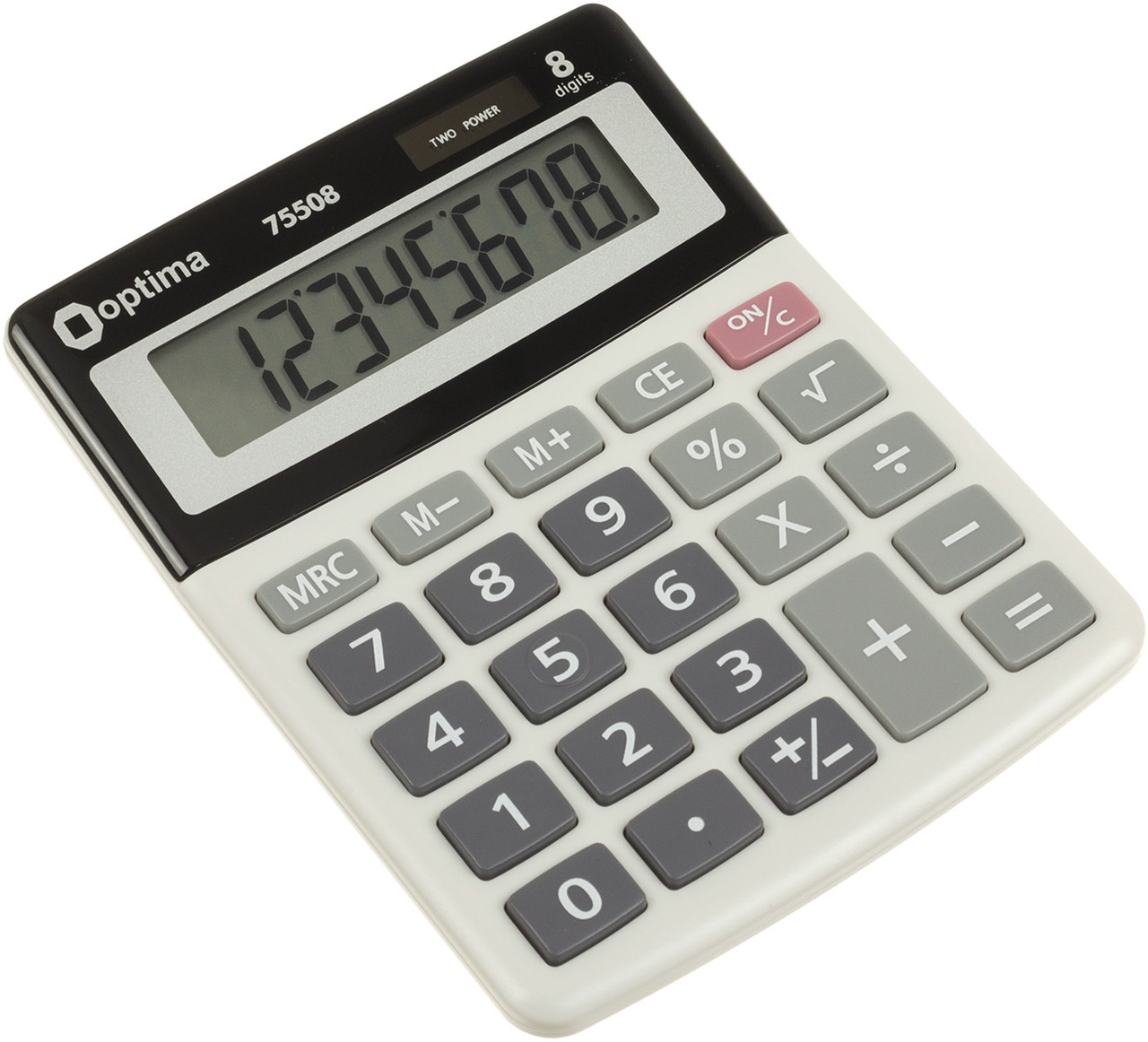
75508
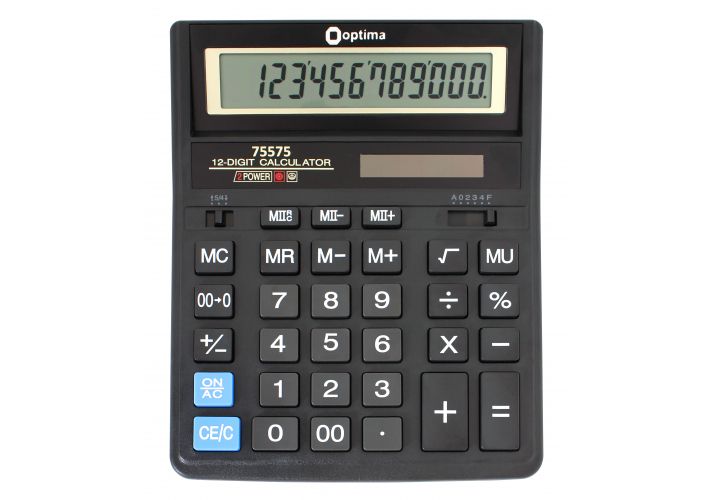
75575
#backword #read #cirillic
указатель на ПЯС
https://www. google.com/search?q=пяс&tbm=isch
Share722-12-2025 15:26:02
Directory of RM_Reserve
09.09.2014 06:24 159 Reserve.log
19.05.2016 02:49 1 907 ReturnFile.vbs
19.05.2016 02:50 1 482 RevFile.vbs
Directory of RM_Reserve\system.sav
07.12.2018 15:59 <DIR> Logs
07.12.2018 15:59 <DIR> util
Directory of RM_Reserve\system.sav\Logs
26.05.2018 15:02 1 232 491 INSTALL_PASS1.log
07.12.2018 15:59 <DIR> OA3
Directory of RM_Reserve\system.sav\Logs\OA3
07.12.2018 04:14 14 291 OA3.Trace.xml
07.12.2018 04:14 482 OA3ChkEdt.log
Directory of RM_Reserve\system.sav\util
07.12.2018 14:43 3 301 184 INSTALL.LOG
-----------------------------------------------------------
file Reserve.log
\system.sav\util\install.log
\System.sav\Logs\OA3\OA3.Trace.xml
\system.sav\ATFPO.ini
\System.sav\Logs\OA3\OA3ChkEdt.log
\System.sav\Logs\INSTALL_PASS1.log
---------
Share822-12-2025 15:26:52
REM ===========================================================================
REM ReturnFile.vbs
REM Bakup file to reverse
REM 2010-01-06
REM ===========================================================================
const CONSOLE_HIDE=0
const CONSOLE_SHOW=1
const CMD_WAIT=true
Const ForReading = 1, ForWriting = 2, ForAppending = 8
set oShell = WScript.CreateObject("WScript.shell")
set oFs = CreateObject("Scripting.FileSystemObject")
set objArgs = Wscript.Arguments
If objArgs.Count <> 3 then
WScript.ECHO "Reverse error args"
WSCript.Quit 1
End If
'Get target disk
outDrive = Wscript.Arguments(2)
if not oFs.FolderExists(outDrive) then
WScript.echo "Can't find drive [" & outDrive & "]"
WScript.Quit 1
end if
'Get source folder
srcPath= Wscript.Arguments(1)
if not oFs.FolderExists(srcPath) then
end if
'Get src log file
inFileName = Wscript.Arguments(0)
set inFile = oFs.OpenTextFile(inFileName, ForReading , True)
' Do While Not inFile.AtEndOfStream
' outWhere = Trim(inFile.ReadLine)
' pos = InStrRev(outWhere, "\")
' if (pos > 0) then
' outPath = outDrive & Left(outWhere, pos)
'
' srcWhere = srcPath & Replace(outWhere, Left(outWhere, pos) , "")
' if oFs.FileExists(srcWhere) then
' wscript.echo "srcWhere= " & srcWhere & " , outPath= " & outPath
' oFs.CopyFile srcWhere, outPath
' end if
' end if
' Loop
Do While Not inFile.AtEndOfStream
outWhere = Trim(inFile.ReadLine)
strtmp = outDrive & outWhere
pos2=InStrRev(strtmp,"\")
outPath = Mid(strtmp, 1, pos2)
srcWhere = srcPath & outWhere
if oFs.FileExists(srcWhere) then
wscript.echo "srcWhere= " & srcWhere & " , outPath= " & outPath
set oShell = wscript.createObject("WScript.Shell")
oShell.run "cmd /c MKDIR " & outPath, CONSOLE_HIDE, CMD_WAIT
oFs.CopyFile srcWhere, outPath
end if
Loop
inFile.Close
Share922-12-2025 15:27:08
REM ===========================================================================
REM Bakup file to reverse
REM ===========================================================================
const CONSOLE_HIDE=0
const CONSOLE_SHOW=1
const CMD_WAIT=true
Const ForReading = 1, ForWriting = 2, ForAppending = 8
set oShell = WScript.CreateObject("WScript.shell")
set oFs = CreateObject("Scripting.FileSystemObject")
set objArgs = Wscript.Arguments
If objArgs.Count <> 3 then
WScript.ECHO "Reserve error args"
WSCript.Quit 1
End If
'Get src disk
srcDrive = Wscript.Arguments(1)
if not oFs.FolderExists(srcDrive) then
WScript.echo "Can't find drive [" & srcDrive & "]"
WScript.Quit 1
end if
'Get output folder
outWhere = Wscript.Arguments(2)
if not oFs.FolderExists(outWhere) then
oFs.CreateFolder(outWhere)
end if
'Get input log file
inFileName = Wscript.Arguments(0)
set inFile = oFs.OpenTextFile(inFileName, ForReading , True)
Do While Not inFile.AtEndOfStream
sName = srcDrive & Trim(inFile.ReadLine)
if (oFs.FileExists(sName)) then
pos1=InStr(sName,"\")
pos2=InStrRev(sName,"\")
strOutFilePath = outWhere & Mid(sName,pos1+1,pos2-pos1)
WScript.ECHO "Src=" & sName & " " & "Dest=" & strOutFilePath
set oShell = wscript.createObject("WScript.Shell")
oShell.run "cmd /c MKDIR " & strOutFilePath, CONSOLE_HIDE, CMD_WAIT
oFs.CopyFile sName, strOutFilePath
end if
Loop
inFile.Close
WSCript.Quit 0
Share1022-12-2025 15:28:40
file OA3ChkEdt.log
-----------------
OEM Activation Tool 3.0
(c) Copyright 2016 Microsoft Corp.
64-bit Version: 10.0.16288.1
Loaded 'DismApi.dll' from system directory.
Edition of the Windows: CoreSingleLanguage
OEM Activation Tool 3.0 has successfully checked that the edition of the
injected product key matches the edition of Windows.
For more information about the tool's requirements, see the OA 3.0 Tool
documentation in the OEM Activation 3.0 - Overview and Usage Guide.
Share1122-12-2025 15:36:13
******************************************************
FBI StartUp at ->Sat May 26 02:57:35 2018<- aka ->1527332255
This should be the first start of FBI - 1.60.31
SM v1.60.31
[02:57:36.134] attempting to merge autotest.ini file defined as ->C:\SYSTEM.SAV\FBI\AUTOTEST.INI
[02:57:36.205] FBI is starting in debug mode ->1
[02:57:36.205] Found SMBIOS...
[02:57:36.282] found type 1 structure...
[02:57:36.329] found type 2 structure...
[02:57:36.376] found type 3 structure...
[02:57:36.423] found type 4 structure...
[02:57:36.517] done counting physical processors...
[02:57:36.595] Successfully raised privileges to allow FBI to restart/shutdown machine
[02:57:36.595] Loading Internal FBI Toolbox functions
[02:57:36.672] LoadFBIKB_NT - FBIKB_NT.SYS load Successful
[02:57:36.672] ...MOSProc module detected
[02:57:36.672] ...MOSProc appears to be done processing
[02:57:36.672] ...importing values from - 'C:\SYSTEM.SAV\FBI\POSTSDV.INI', and setting it active state overrides
[02:57:36.672] Loading Internal FBI Script functions
[02:57:36.672] FBIDATE.DLL did not load
[02:57:36.672] Done Loading FBI Environment
[02:57:37.801] AllowSetForegroundWindow succeded
[02:57:37.895] LockSetForegroundWindow succeded - LOCKED
[02:57:39.929] No Startup Delay defined
[02:57:39.929] Task Manager thread is starting, current section is ->
[02:57:39.929] No delay defined...
[02:57:40.138] Task Manager thread is starting, current section is ->FBI.Init.General
[02:57:40.138] No delay defined...
[02:57:40.138] Processing ->CMD1 ->CMD.exe /c c:\system.sav\ExitProc\UpdERROR.CMD 941 "Entered PASS1"
[02:57:43.059] Processing ->CMD2 ->CheckMachine
[02:57:43.059] Processing ->CMD3 ->SetupAutomation
[02:57:43.059] ...This requires ReadUIAData to have been ran.
[02:57:43.059] ...This requires DetectOSImage to have been ran.
[02:57:43.059] Processing ->CMD4 ->InitProgressBar
[02:57:43.075] Processing ->CMD5 ->HideActivity
[02:57:43.075] Processing ->CMD6 ->ShowActivity
[02:57:44.239] Processing ->CMD7 ->SetVar(FBITB.ProcessTools,ErrorFlagPath,C:\CTOERROR.FLG)
[02:57:44.239] Processing ->CMD8 ->C:\system.sav\fbi\cNBPANIC.BTO
[02:57:44.239] c:\system.sav\fbi\cnbpanic.bto
[02:57:44.239] cmd.exe /c c:\System.sav\fbi\CheckForErrorFlag.cmd
[02:57:47.183] Processing ->CMD9 ->SetVar(FbiData,ProcessState,InMiniWindows)
[02:57:47.183] Processing ->CMD10 ->SetVar(FBIData,BTOName,C:\appl.zip\ImageTweaks)
[02:57:47.183] Processing ->CMD11 ->ProcessBTOName
[02:57:47.183] c:\appl.zip\imagetweaks
[02:57:47.183] c:\appl.zip\imagetweaks\W10RS4.bto
[02:57:47.237] @REM ======================================================================
[02:57:47.237] @REM Script : W10RS4.bto
[02:57:47.237] @REM Deliverable : Windows 10 PIN AddOn ReD - CPS
[02:57:47.237] @REM Description :
[02:57:47.237] @REM This will process some script[s] for Win 10.
[02:57:47.237] @REM NOTEs :
[02:57:47.237] @REM ======================================================================
[02:57:47.237] @REM RS4 tweaks to perform different process from RS3
[02:57:47.237] @SingleObj cmd.exe /c C:\Appl.zip\ImageTweaks\RS4tweak.cmd
[02:57:47.237] *** PROCESS INFORMATION START ***
[02:57:47.237] Num ProcID New Ignore Module
[02:57:47.237] 1 [0x0000, 0] N N <[System Process]>
[02:57:47.237] 2 [0x0004, 4] N N <System>
[02:57:47.237] 3 [0x0068, 104] N N <Registry>
..........
.........
[04:38:25.986] @ENDIF
[04:38:26.002] @REM ======================================================================
[04:38:26.002] @REM END of ZZEnable.bto
[04:38:26.002] @REM ======================================================================
[04:38:27.018] c:\appl.zip\cleanup.eue\ZZZTDCU2_Wx.BTO
[04:38:27.018] @REM ======================================================================
[04:38:27.018] @REM Script : ZZZZTDCU2.BTO
[04:38:27.018] @REM Deliverable : TFS - MS Windows PIN Process - TDC
[04:38:27.033] @REM Description :
[04:38:27.033] @REM Clean up unnecessary file(s)
[04:38:27.033] @REM
[04:38:27.033] @REM This is for Win7/8.1
[04:38:27.033] @REM ======================================================================
[04:38:27.033] @REM --------------------------------------------------------
[04:38:27.033] @REM Clean up unnecessary files from Hou during FBI unbundling
[04:38:27.033] @REM --------------------------------------------------------
[04:38:27.033] @AddToDeleteList C:\System.sav\Util\CloseWIN.exe
[04:38:27.033] @AddToDeleteList C:\System.sav\Util\MergeINI.exe
[04:38:27.033] @AddToDeleteList C:\System.sav\Util\MergeCIA.cmd
[04:38:27.049] @AddToDeleteList C:\System.sav\Util\cpqci.dll
[04:38:27.049] @MOVE C:\System.sav\Logs\PreinChk.log C:\System.sav\Logs\PreinChk_FBI.log
[04:38:27.049] WARNING-=-CmdMove() - Error=2, Не удается найти указанный файл.
[04:38:27.049] WARNING-=-CmdMove() - src=C:\System.sav\Logs\PreinChk.log does not exist
[04:38:27.049] @AddToDeleteList C:\System.sav\PreinChk.log
[04:38:27.049] @AddToDeleteList C:\Win8.32
[04:38:27.049] @AddToDeleteList C:\Win8.64
[04:38:27.049] @AddToDeleteList C:\System.sav\Util\CPQREG.EXE
[04:38:27.049] @AddToDeleteList C:\System.sav\Util\CPU64.exe
[04:38:27.049] @AddToDeleteList C:\System.sav\Util\BNBProc.exe
[04:38:27.049] @AddToDeleteList C:\System.sav\Util\BNBProc.ini
[04:38:27.049] @AddToDeleteList C:\System.sav\Util\cvacompg.exe
[04:38:27.064] @AddToDeleteList C:\System.sav\Util\DelDir.exe
[04:38:27.064] @AddToDeleteList C:\System.sav\Util\DeTekOS2.exe
[04:38:27.064] @AddToDeleteList C:\LPs
[04:38:27.064] @AddToDeleteList C:\MCPP
[04:38:27.064] @AddToDeleteList C:\3G
[04:38:27.064] @AddToDeleteList c:\System.sav\Util\devcon.exe
[04:38:27.064] @AddToDeleteList c:\System.sav\Util\devcon64.exe
[04:38:27.064] @REM --------------------------------------------------------
[04:38:27.064] @REM Clean up unnecessary files if the image is for customer
[04:38:27.064] @REM --------------------------------------------------------
[04:38:27.064] @IfNotFile( C:\System.sav\Flags\EnableDebugMode.flg )
....
.....
[04:43:22.937] Processing ->CMD194 ->SetVar(FbiData,ProcessState,Done)
[04:43:22.938] Processing ->CMD195 ->SetVar(FBITB.GeneralTools,SectionToClean,Description)
[04:43:22.938] Processing ->CMD196 ->CleanCIASection
[04:43:22.938] Processing ->CMD197 ->SetVar(FBITB.GeneralTools,SectionToClean,Configuration)
[04:43:22.938] Processing ->CMD198 ->CleanCIASection
[04:43:22.938] Processing ->CMD199 ->SetVar(FBITB.GeneralTools,SectionToClean,UIA)
[04:43:22.938] Processing ->CMD200 ->CleanCIASection
[04:43:22.938] Processing ->CMD201 ->C:\system.sav\bbv\PE_EXEC.BTO
[04:43:22.938] c:\system.sav\bbv\pe_exec.bto
[04:43:22.969] @REM ======================================================================
[04:43:22.969] @REM Script : PE_EXEC.BTO
[04:43:22.969] @REM Deliverable: Windows 7 SP1 PIN Tweaks - TDC
[04:43:22.969] @REM Description:
[04:43:22.969] @REM This will be used for any tweaks that will be launched before
[04:43:22.969] @REM capturing User partition image under WinPE.
[04:43:22.969] @REM ======================================================================
[04:43:22.969] @REM ----------------------------------------------------------------------
[04:43:22.969] @REM Split big files into small pieces before capturing image due to the
[04:43:22.969] @REM single file size limitation on Converyor & Prism server. It's to
[04:43:22.969] @REM prevent the possible data transfer issue with big files through the
[04:43:22.969] @REM internet. Some software components release with big files and some
[04:43:22.969] @REM may create big files during the software installation.
[04:43:22.985] @REM ----------------------------------------------------------------------
[04:43:22.985] @IfFile(C:\System.sav\util\BFSplit.cmd)
[04:43:23.001] Lines will be executed
[04:43:23.001] @SingleObj CMD.exe /c C:\System.sav\util\BFSplit.cmd
[04:43:23.001] *** PROCESS INFORMATION START ***
...........
[05:02:44.869] 28 [0x03C4, 964] N Y <conhost.exe>
[05:02:44.869] 29 [0x0550,1360] N Y <vds.exe>
[05:02:44.869] Current Process Count: [29]; Current Filtered Count: [11]
[05:02:44.869] *** PROCESS INFORMATION END ***
[05:02:44.869] @Else
[05:02:44.869] @EndIf
[05:02:44.869] @EndIf
[05:02:44.869] @REM ======================================================================
[05:02:44.869] @REM
[05:02:44.869] @REM FACTORY GOLDEN MASTER IMAGE IS READY
[05:02:44.869] @REM
[05:02:44.869] @REM ======================================================================
[05:02:44.869] @EndIf
[05:02:44.869] @REM backup CIA.ini
[05:02:44.869] @COPY C:\System.sav\Util\CIA.ini C:\System.sav\Logs\PINPROC\CIA.FBI1GS.ini
[05:02:44.884] @REM ======================================================================
[05:02:44.884] @REM END of diskut.bto
[05:02:44.884] @REM ======================================================================
[05:02:44.884] @REM ======================================================================
[05:02:44.884] @REM
[05:02:44.884] @REM
[05:02:44.884] @REM PASS 1 completed.
[05:02:44.884] @REM
[05:02:44.884] @REM
[05:02:44.884] @REM ======================================================================
[05:02:45.892] Processing ->CMD209 ->EnableMouseKeyboard
[05:02:45.892] Processing ->CMD210 ->SetVar(FbiData,ProcessState,Done)
[05:02:45.892] Processing ->CMD211 ->HideActivity
[05:02:46.033] FBISM no more sections to process, must be done - have a nice day...
[05:02:46.244] NOTICE: FBI is exiting without restarting/shutingdown the computer
[05:02:46.524] FBIDMLOG.DLL - Shutting down the OM window...
FBI Shutting down at ->Sat May 26 05:02:58 2018
<- aka ->1527339778
Run time ->1208
Total Run time ->6471
Total time since first start ->0
Share1222-12-2025 15:38:15
[04:38:25.939] @REM NOTEs :
[04:38:25.939] @REM original deliverable is "Common Mobile Toolbox"
[04:38:25.955] @REM ======================================================================
[04:38:25.955] @IFNOTFILE(C:\System.Sav\Logs)
[04:38:25.955] Lines will be skipped
[04:38:25.955] @ENDIF
[04:38:25.955] @AddToDeleteList C:\System.Sav\Util\MOBDEV
[04:38:25.970] @IFFILE(C:\System.Sav\Util\MOBDEV\ENABLE.CMD)
[04:38:25.986] Lines will be skipped
[04:38:25.986] @ENDIF
[04:38:26.002] @REM ======================================================================
[04:38:26.002] @REM END of ZZEnable.bto
[04:38:26.002] @REM ======================================================================
[04:38:27.018] c:\appl.zip\cleanup.eue\ZZZTDCU2_Wx.BTO
[04:38:27.018] @REM ======================================================================
[04:38:27.018] @REM Script : ZZZZTDCU2.BTO
[04:38:27.018] @REM Deliverable : TFS - MS Windows PIN Process - TDC
[04:38:27.033] @REM Description :
[04:38:27.033] @REM Clean up unnecessary file(s)
[04:38:27.033] @REM
[04:38:27.033] @REM This is for Win7/8.1
[04:38:27.033] @REM ======================================================================
[04:38:27.033] @REM --------------------------------------------------------
[04:38:27.033] @REM Clean up unnecessary files from Hou during FBI unbundling
[04:38:27.033] @REM --------------------------------------------------------
[04:38:27.033] @AddToDeleteList C:\System.sav\Util\CloseWIN.exe
[04:38:27.033] @AddToDeleteList C:\System.sav\Util\MergeINI.exe
[04:38:27.033] @AddToDeleteList C:\System.sav\Util\MergeCIA.cmd
[04:38:27.049] @AddToDeleteList C:\System.sav\Util\cpqci.dll
[04:38:27.049] @MOVE C:\System.sav\Logs\PreinChk.log C:\System.sav\Logs\PreinChk_FBI.log
[04:38:27.049] WARNING-=-CmdMove() - Error=2, Не удается найти указанный файл.
[04:38:27.049] WARNING-=-CmdMove() - src=C:\System.sav\Logs\PreinChk.log does not exist
[04:38:27.049] @AddToDeleteList C:\System.sav\PreinChk.log
[04:38:27.049] @AddToDeleteList C:\Win8.32
[04:38:27.049] @AddToDeleteList C:\Win8.64
Share1322-12-2025 15:39:05
Привет русскоговорящему дядяшке Hou!
Share1422-12-2025 15:42:11
Это были файлы с нового купленного ноутбука HP в сети укро-магазинов MOYO примерно в 2019 году с установленным Windows 10 с завода
Share1522-12-2025 15:44:46
"Hou" (后/侯) in Chinese can refer to an ancient royal title (King/Queen/Marquis), a surname, a currency unit (毫), or a legendary creature (犼). In Channel Islands/Norman English, "-hou" is a suffix for small islands (like Stockholm), while in Russian, "hou" can mean a shout or cry.
Chinese Contexts:
Title (后 - Hòu): An ancient title for rulers, later used for Queens (like Empress).
Title (侯 - Hóu): A noble rank, often translated as "Marquis".
Surname: A common Chinese surname, often a descendant of nobility.
Currency (毫 - Háo): A subdivision of the Hong Kong dollar.
Mythology: A mythical creature (Denglong).
Other Meanings:
Suffix (-hou): In Norman/Channel Islands names, meaning "small island" (e.g., Sark's "Petit Port" is on "Petit Houmet").
Russian: "hou" (ху) can mean a shout or cry.
To give a more specific answer, more context is needed (e.g., "Hou Minghao" is a Chinese actor, or "Hou Yifan" is a chess player).
Share1622-12-2025 15:45:51
«Хоу» (后/侯) на китайском языке может относиться к древнему королевскому титулу (король/королева/маркиз), фамилии, денежной единице (毫) или легендарному существу (犼). На Нормандском английском языке «-hou» является суффиксом для небольших островов (например, Стокгольма), а в русском «hou» может означать крик или плач.
Китайский контекст:
Титул (后 - Хоу): древний титул правителей, позже использовавшийся для королев (например, императрицы).
Титул (侯 - Хоу): дворянский титул, часто переводимый как «маркиз».
Фамилия: Распространенная китайская фамилия, часто принадлежащая потомкам знати.
Валюта (毫 - Хао): подразделение гонконгского доллара.
Мифология: Мифическое существо (Дэнлун).
Другие значения:
Суффикс (-hou): в названиях Нормандских/нормандских островов означает «маленький остров» (например, «Пти-Порт» Сарка находится на «Пти-Уме»).
В русском языке «хоу» (ху) может означать крик или плач.
Чтобы дать более конкретный ответ, необходимо больше контекста (например, «Хоу Минхао» — китайский актер или «Хоу Ифань» — шахматист).
Share1723-12-2025 10:50:42
Американские деньги печатают уже все кому не лень.
#FRS
Share1803-01-2026 16:46:49
#get #status #operation #similar #getlink https://filmix.my/film/triller/1458-v-g … -1990.html
Share1907-01-2026 17:14:19
#sanction #Ad #Vertis #Ment!
#unsigned dword cashflow
Как мы можем помочь?
Digital Caramel Inc.Tel.: +7(495) 108-54-63 info@digitalcaramel.comArmenia Monetrise LLC Tax ID: 00925653 ул․ Анастаса Микояна, 2/2, 185 Ереван 0045
USA Digital Caramel Inc.Tax ID: 37-19966565420 Alaire Vie Dr. Fair Oaks CA 95628
Estonia Weprodigi OÜReg. code: 16346611 Harju maakond, Tallinn, Kesklinna linnaosa, Valge tn 13, 11415
Share2007-01-2026 18:15:07
#MITM #tracert #detected!
Share2107-01-2026 19:58:00
Вот так и получилось, как "блондинка", с закрытыми глазами устроиться в Ленгли, мне маленькому мальчику )))))))
BALENCIAGA -> CIA + BALENGA ( B -> A - lenga ( langley )
Еще есть исполнительница музыки Ваенга. )))))
AGA IS NE "LAB" )))))
"deep house" - дом госДЕПА.
Что там в Живой Этике упоминалось про "наши лаборатории"?
https://www.youtube.com/watch?v=Yb65TiOL31g

Share2207-01-2026 20:09:06
Разгадывать как модные дома на показах "сливают" нужную инфу фенеботя одеждой и всем во что одеты и в руках?
Это у кого-то Бершка,а у некоторые это Вершки, те. Сливки - сливы .... не фрукты, а процесс отправки куда то информации.

Share2307-01-2026 20:12:04
Короче, для расшифровки нужен фактурный материал, по одной именно эти, из каждого модного дома, в типичной конфигурации.
Нужно внимательно рассматривать со всех сторон.
)))))))))))))))))))))))))))))))))))))))))))))
Share2412-01-2026 23:27:57
#NSA #get #trace #filelist
INPUT HIVE TYPE ARC MD5 dedb8aba30ef01c71c13f557ab0272ea SHA1 821aeb3b9ec09bfcd18b33ccd5f30251211b0e62 CRC32 682e1920 SHA-256 72d7f85bcf6e7e39482ab7796cfd4558cbade5638df8be6cde83cf923994da1e SHA-512 19f64152e142083772e089f5513aecefe2203ebc48976502548e11b017609b1f5b47610e701d6cb723ca72143f548a4b192541eb719ba21f57d2beea6c33a642 SHA-384 6dcaa37a0a9dfbababbecddaa651ed7232f14acda83395b95febbee7da748d736725045c291f0595fed50ac31cc956a5
Share2513-01-2026 09:29:55

1/1
